Posts
1311Following
HiddenFollowers
Hiddenmiifox
miifoxAnd yes, that second photo can be viewed on a 3ds; needless to say the pentax K1's (damn i'm brand-loyal) images are miles ahead of the cheap 640x480 specials the 3ds has.
photo of a fursuit girl. the sa…
the same shot; but in a format …
DanCrescentWolf
dancrescentwolf@pounced-on.meSHE'S DOOOOONE
Here ya go guys, new Xenia wallpaper!!
Had a blast working on this, hope I can do more soon! x3
Download the free 4k resolution desktop wallpaper here:
https://ko-fi.com/s/594c1ab898
Tips are, of course, highly appreciated and might result in me making more free wallpapers for you guys! :3
Really hope you like it OwO
.
tillian 🦊  ACAB
ACAB
mynameistillian@plush.city
people consist around 72% out of water, but i consist out of caffeine, ibuprofen, shawarma, and pure spite
Charlotte  /Cinny
/Cinny 



charlotte
this is fossslop you only like it because it’s freely available on your operating system
snow 

snow@cofe.rocks
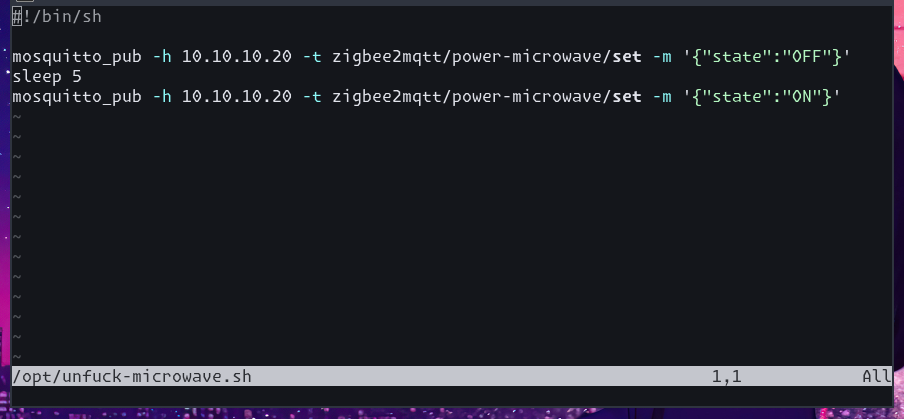
ppl always complain that the clock on my microwave never shows the right time bcs i cant be assed to set it manually
so now i have an unfuck-microwave.sh cronjob which briefly kills its power every day at midnight
Botch Frivarg
deetwenty@todon.nlOne way to make this wolf very happy? Big inflatables!
Fursuit: Sarah Cat Fursuits (https://www.sarahcatfursuits.com/ )
Obscura, Cheetah
CheetahObscura@meow.socialA sassy chee to brighten your timeline for a moment. 💜🧡
Arts by Reina (https://vipercrown.com/)
Omez
OMEZ@mastodon.artStefan wants to be your friend! Little character idea i came up with in a recent stream. He is a stray and looking for friends and maybe a home. Be nice to him! #furryart
miifox
miifoxShow content
pentax: haha 67
OMG. -froot bug resurfaced. https://seclists.org/oss-sec/2026/q1/89
I see the headlines, "10 years old bug".
My friends, this bug is older. Much older. Not this particular instance, but it is a classical mistake to make. It's a command line injection when calling the login executable.
Some people point to CVE-2007-0882. Solaris had that, almost 20 years ago.
But it's even older than that. It's so old it predates the CVE system. I don't remember exact dates, but we popped Linux and AIX boxes with that, mid 90s.
But it is *even older* than that. Have a look at System V R4, ©1990, getty calling login with unsanitized input:
But how deep does the rabbit hole go? When was this bug introduced?
Getty called login with user input since the dawn of time (UNIX V2, 1972):
https://www.tuhs.org/cgi-bin/utree.pl?file=V2/cmd/getty.s
But this predates command line arguments in login:
https://www.tuhs.org/cgi-bin/utree.pl?file=V2/cmd/login.s
So, when did this particular command line feature of login appear?
In the BSD universe, -f was introduced with POSIX compatibilitiy in 4.3BSD-Reno:
https://www.tuhs.org/cgi-bin/utree.pl?file=4.3BSD-Reno/src/usr.bin/login/login.c
But someone paid attention and filtered out user names starting with - in getty:
https://www.tuhs.org/cgi-bin/utree.pl?file=4.3BSD-Reno/src/libexec/getty/main.c
RCS timestamp says 6/29/1990, so same age as SysV R4.
The original 4.3BSD (1986) doesn't filter the user name:
https://www.tuhs.org/cgi-bin/utree.pl?file=4.3BSD/usr/src/etc/getty/main.c
And it does have a -r option in login:
https://www.tuhs.org/cgi-bin/utree.pl?file=4.3BSD/usr/src/bin/login.c
Exploitable? No idea, argv processing might be a problem. I'll find out another day.
In conclusion: bug existed since 1990, it's so easy to make when implementing POSIX that it keeps resurfacing, and at least one person in Berkeley knew since day 0.
evacide
evacide@hachyderm.ioDo not store your Bitlocker encryption keys on Microsoft's servers if your threat model includes governments or law enforcement. As this article points out, this is the result of a design choice Microsoft made. It didn't have to be this way.
mjdxp
mjdxp@labyrinth.zoneClep-Karb @ Home 🏠
karb@bark.lgbt"Noodle Dragon in front of noodle shop? Now all I need is my noodle bowl to get comfy. Do you want to join?"
📍 Suitwalk Offenburg January
📸 @Setsu
#FursuitFriday #Dragon
miifox
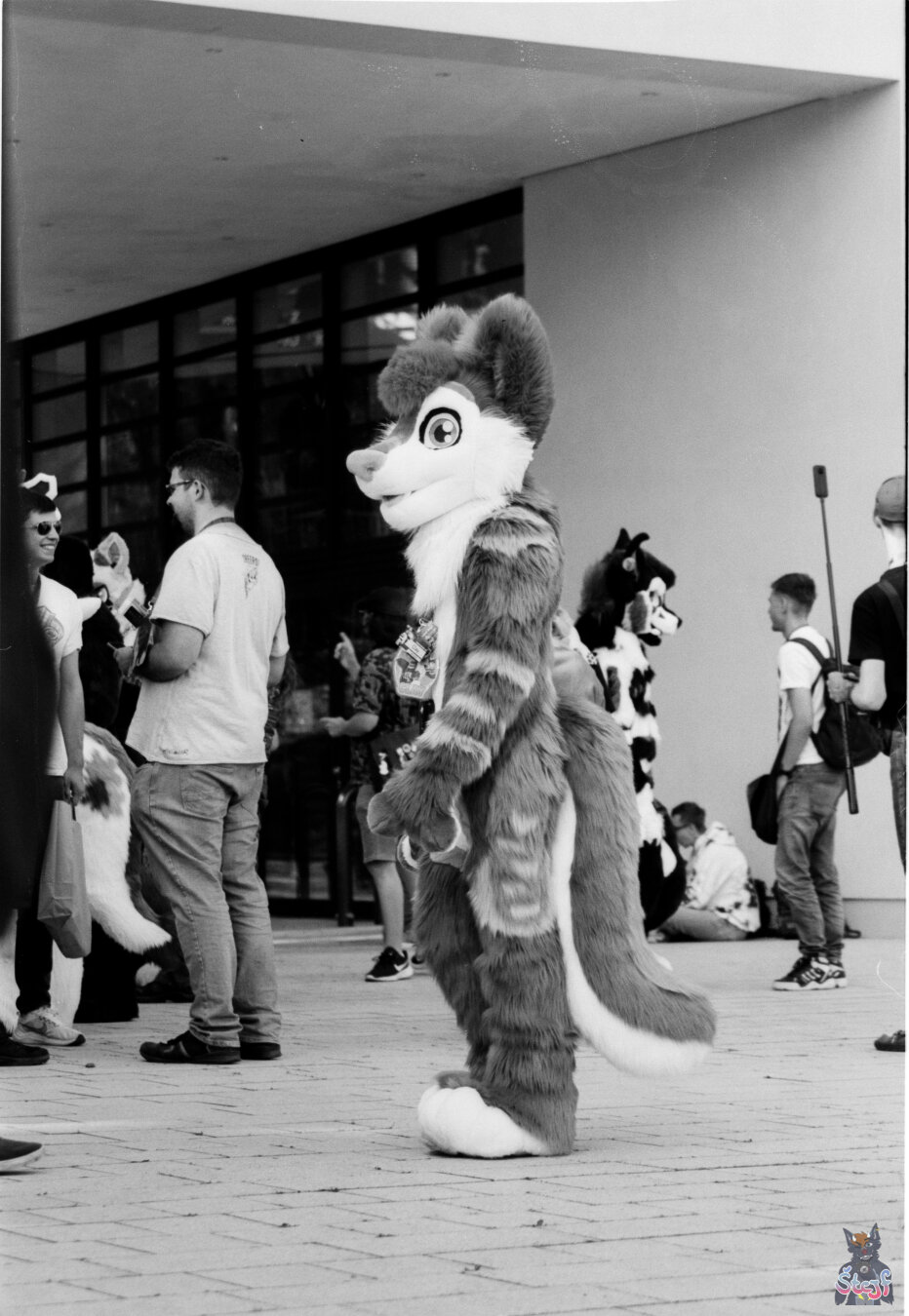
miifoxPhoto by @botchFrivarg on my #gl690 #analogPhotography
it's a girl fox falling over on…
it's a girl fox riding the plus…
Charlotte  /Cinny
/Cinny 



charlotte
dutch trains are digital. either you arrive approximately on time or you do not arrive at all
german trains are satanic. you will eventually arrive but the price in terms of time or sanity may be greater than you intended